Category: cybersecurity
You are viewing all posts from this category, beginning with the most recent.
🔒 Big improvements to calls in Signal: call links
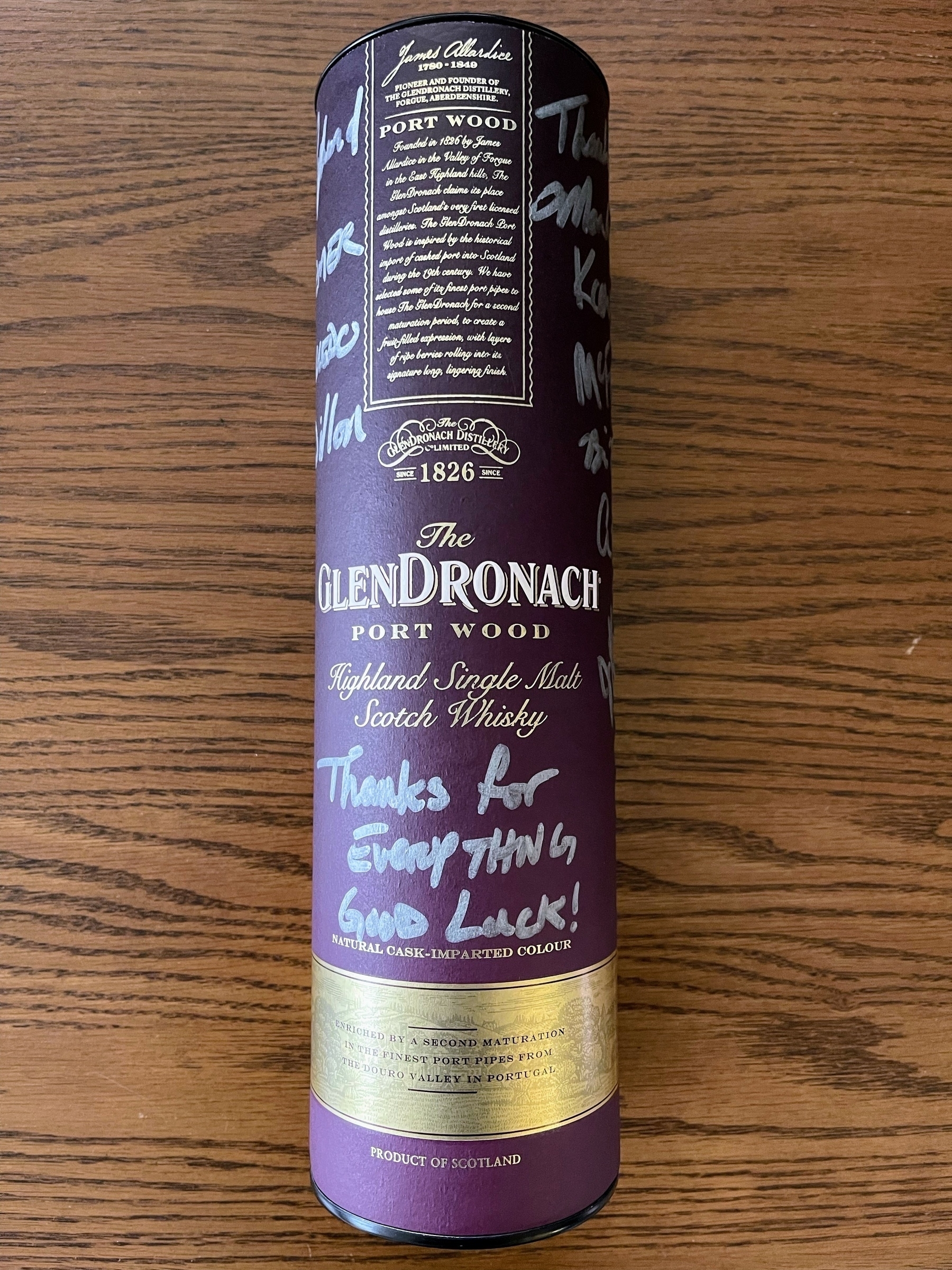
🔒🥃 Hey, you know how security teams are the worst and nobody wants to work with them?
Anyway, this is a signed going away present from the engineering platform and architecture leaders.
Definitely a keeper, even after it’s empty.
🔒 I’m at the CSO Conferencece and Awards.
Tomorrow, my team will be accepting a CSO50 award for our security automation platform that supports 4000 engineers and 7000 applications.
I’ve since left the company, but am here supporting my previous team. Proud of them!
🔒 Banks: practice internet safety!
Also banks: we won’t let you login if you are blocking junk in your browser or using a VPN
🔒 The opportunity: application threat modeling & secure design review is one of the highest value appsec/prodsec activities, but is hard to implement efficiently and at scale.
A bad solution: provide a long list of controls that need to be checked each time
A better solution: generate relevant security requirements automatically based on what’s being built
Met with primesec yesterday, and this is what they are trying to do! They are using LLM to read what’s in your user stories (etc.), summarizing the work for the security team, and injecting specific security control requirements.
If this catches even a small portion of the real requirements, it would be a major uplift for teams both from a security and efficiency perspective. Looking forward to checking it out.
🔒 Met with the folks from Pangea yesterday.
Looks like it could be an interesting solution for:
- small developer orgs that don’t have time or expertise to deal with common security needs
- large developer orgs that need consistency, scale, and governance of their security capabilities
I’m at AppSec San Francisco this week.
Mute that “🔒” tagmoji if you don’t want to hear about it.
Send me a message if you want to meet up.
🔒 OSS backdoors: the folly of the easy fix - lcamtuf’s thing
Even when it comes to lesser threats, the bottom line is that we have untold trillions of dollars riding on top of code developed by hobbyists. The companies profiting from this infrastructure can afford to thoroughly vet and monitor key dependencies on behalf of the community. To be sure, a comprehensive solution would be a difficult and costly undertaking — but it’s not any harder or costlier than large language models or self-driving cars.